Cybersecurity researchers at Check Point have attributed a new Bring Your Own Vulnerable Driver (BYOVD) campaign to the threat actor known as Silver Fox, who is abusing a previously unknown vulnerable driver in WatchDog Anti-malware to disable endpoint security solutions and deliver ValleyRAT malware.
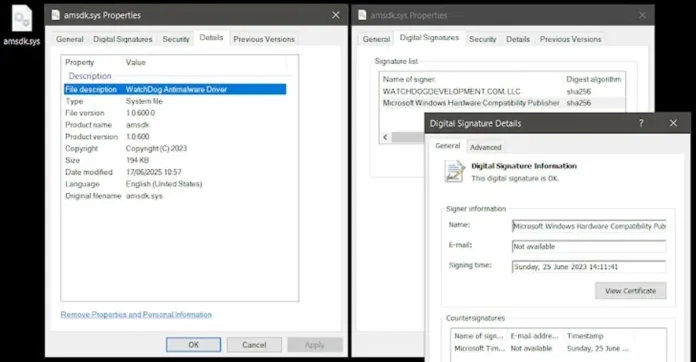
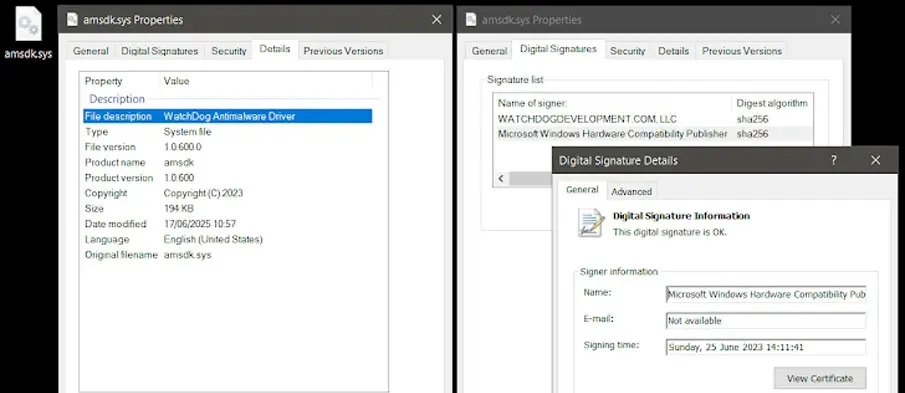
The exploited driver, “amsdk.sys” (v1.0.600), is a Microsoft-signed, 64-bit Windows kernel driver built on the Zemana Anti-Malware SDK. Check Point noted, “This driver, built on the Zemana Anti-Malware SDK, was Microsoft-signed, not listed in the Microsoft Vulnerable Driver Blocklist, and not detected by community projects like LOLDrivers.”
The attack leverages a dual-driver approach — using the known vulnerable Zemana driver for Windows 7 systems and the unlisted WatchDog driver for Windows 10 and 11. The driver flaws allow attackers to terminate arbitrary processes without checking Protected Process Light (PPL) status and escalate privileges locally, granting complete access to the driver.
First observed in May 2025, the campaign uses a sophisticated all-in-one loader that integrates anti-analysis techniques, driver exploits, antivirus-killer logic, and a ValleyRAT downloader. “Upon execution, the sample performs a few common anti-analysis checks, such as Anti-VM, Anti-Sandbox, hypervisor detection, and others,” Check Point said, aborting execution if analysis is detected. The final payload, ValleyRAT, grants remote control over infected hosts.
Following responsible disclosure, WatchDog released a patched driver (v1.1.100) to fix local privilege escalation by tightening its DACL. However, the process termination issue remains unresolved. Attackers quickly adapted by flipping a single byte in the driver’s unauthenticated timestamp field — preserving Microsoft’s signature while bypassing hash-based blocklists.
Check Point warned, “This campaign demonstrates how threat actors are moving beyond known weaknesses to weaponize unknown, signed drivers—a blind spot for many defense mechanisms.”
Silver Fox, also known as SwimSnake or UTG-Q-1000, has been active since 2022, primarily targeting Chinese-speaking users via phishing, fake software installers, and trojanized open-source tools. Its Finance Group sub-cluster specifically attacks enterprise financial teams, using phishing lures tied to tax audits and subsidy notices to steal credentials and drain funds.
QiAnXin described the group as “one of the most active and aggressive cybercrime groups in China in recent years,” with operations combining espionage, malware-driven remote control, and organized financial fraud.