Cybersecurity researchers have uncovered key details about ERMAC 3.0, the latest iteration of an Android banking trojan, revealing extensive data theft capabilities and significant weaknesses in its backend infrastructure. The malware, which targets over 700 banking, shopping, and cryptocurrency apps, represents a notable evolution in mobile cybercrime.
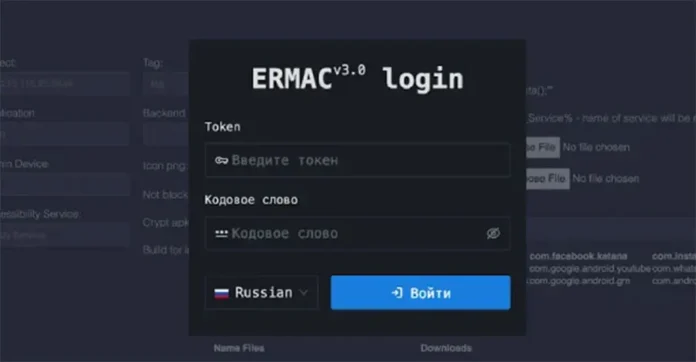
In a report by Hunt.io, researchers disclosed they had accessed the complete source code of the malware-as-a-service (MaaS) variant from an open directory hosted on 141.164.62[.]236:443. The leak exposed the entire ERMAC 3.0 ecosystem, including its PHP-Laravel backend, React frontend, Golang-based exfiltration server, and the Android builder panel used to configure malware campaigns.
ERMAC, first identified in 2021 by ThreatFabric, is attributed to the threat actor “DukeEugene” and is considered an evolution of earlier Android malware families like Cerberus and BlackRock. ERMAC’s lineage also connects it to other modern malware strains, including Hook (ERMAC 2.0), Pegasus, and Loot.
Key components of the ERMAC 3.0 architecture include:
Backend C2 Server: Used to manage victim devices and extract compromised data such as SMS logs and app credentials.
Frontend Panel: Enables attackers to issue commands, control overlays, and interact with infected devices.
Exfiltration Server: A Golang-based system for siphoning stolen data.
Android Backdoor: Written in Kotlin, this implant collects sensitive data and executes commands, while avoiding devices in CIS (Commonwealth of Independent States) countries.
ERMAC Builder: Customizes malware builds by allowing operators to input app names, server addresses, and configurations.
ERMAC 3.0 introduces enhanced form injection techniques, AES-CBC encrypted communications, and a revamped command-and-control panel to boost its stealth and functionality.
However, the leaked infrastructure also exposes serious security flaws in ERMAC’s design. These include a hardcoded JWT secret, static admin bearer token, default root credentials, and open admin panel registrations—vulnerabilities that defenders can exploit to track or disable ongoing operations.
The revelation underscores both the sophistication and fragility of modern mobile malware ecosystems and provides cybersecurity professionals with valuable intelligence for proactive defense.