An unidentified South Korean ERP vendor’s update server has been compromised to distribute a Go-based backdoor known as Xctdoor. The AhnLab Security Intelligence Center (ASEC), which discovered the breach in May 2024, did not attribute it to a specific threat actor or group. However, they highlighted similarities with Andariel, a subset of the notorious Lazarus Group. These parallels stem from previous instances where the North Korean adversary used ERP solutions to disseminate malware like HotCroissant (known as Rifdoor) in 2017, inserting malicious code into software update programs.
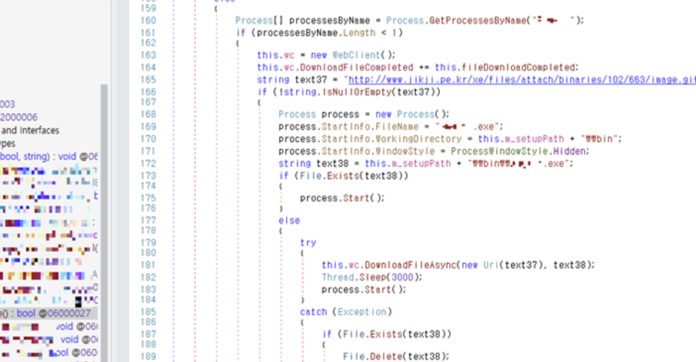
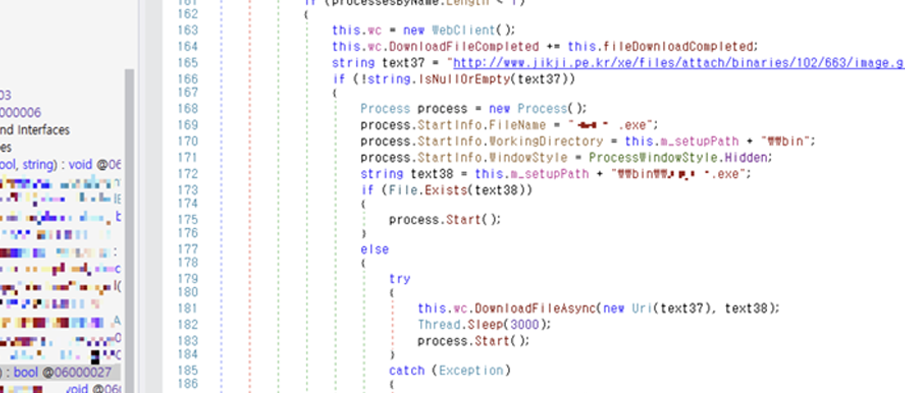
In the recent incident investigated by ASEC, the compromised executable was altered to execute a DLL file from a specified path using the regsvr32.exe process instead of launching a downloader.The DLL file, Xctdoor, is capable of stealing system information such as keystrokes, screenshots, and clipboard content, and executing commands issued by the attacker. According to ASEC, Xctdoor communicates with the command-and-control server via the HTTP protocol, with packet encryption utilizing the Mersenne Twister (MT19937) and Base64 algorithms.
Another component in the attack is a malware called XcLoader, which acts as an injector responsible for injecting Xctdoor into legitimate processes like “”. ASEC also reported instances where poorly secured web servers have been compromised since at least March 2024 to install XcLoader. Concurrently, a North Korea-linked threat actor identified as Kimusky has been observed using a previously undisclosed backdoor called HappyDoor, operational since July 2021. The attack vectors for distributing this malware involve spear-phishing emails containing a compressed file. Upon execution, an obfuscated JavaScript or dropper creates and runs HappyDoor alongside a decoy file.
HappyDoor, also executed via regsvr32.exe, communicates with a remote server over HTTP to facilitate data theft, file downloads/uploads, and self-update/termination functionalities. This activity aligns with a significant malware distribution campaign attributed to the Konni cyber espionage group (also known as Opal Sleet, Osmium, or TA406). They targeted South Korea using phishing tactics that impersonate national tax services to deploy malware capable of exfiltrating sensitive information, as noted by security researcher Idan Tarab.