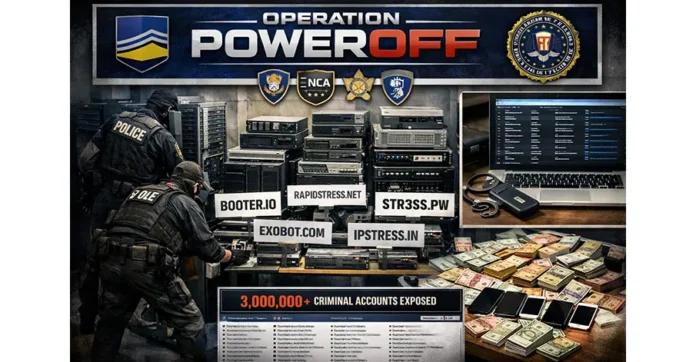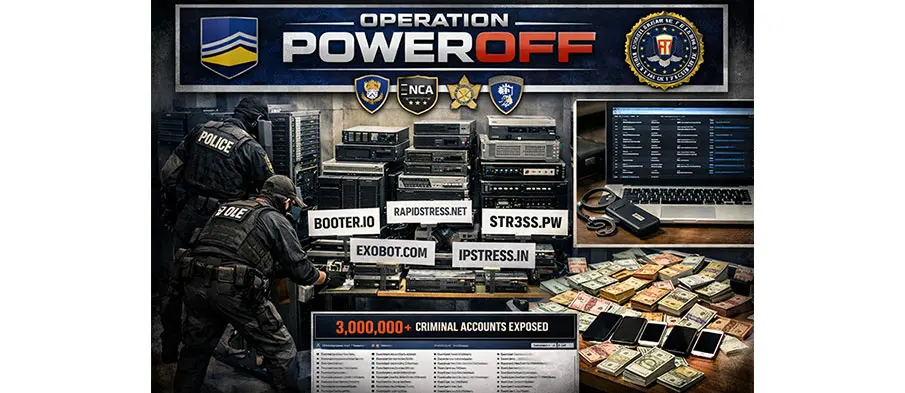
A coordinated international law enforcement effort has led to the takedown of 53 domains linked to distributed denial-of-service (DDoS) for-hire services, marking a significant step in the ongoing fight against cybercrime. The operation, known as Operation PowerOFF, targeted platforms that enable individuals to launch cyberattacks without requiring advanced technical expertise, making such attacks widely accessible.
The action, carried out on April 13, 2026, involved authorities from 21 countries working together to dismantle the infrastructure supporting these illegal services. As part of the crackdown, officials also arrested four individuals and executed over 24 search warrants, highlighting the scale and coordination of the effort.
In addition to enforcement actions, authorities identified and contacted more than 75,000 individuals suspected of using DDoS-for-hire platforms. These users received warning emails and letters, signaling a shift toward both disruption and prevention strategies aimed at discouraging future cyberattacks.
The operation also involved the seizure of servers, databases, and other technical infrastructure that powered these services. By dismantling this backend ecosystem, law enforcement agencies were able to disrupt the operational capabilities of cybercriminal networks and prevent further misuse. The seized data further enabled investigators to trace millions of user accounts connected to such activities, strengthening global intelligence-sharing efforts.
DDoS-for-hire services, often referred to as “booter” or “stresser” platforms, have become one of the most accessible forms of cybercrime. These services allow users with minimal technical knowledge to overwhelm websites and online systems, causing widespread disruption to businesses, government platforms, and digital services.
As Operation PowerOFF moves into its prevention phase, authorities are expanding efforts to curb future misuse through awareness campaigns and proactive interventions. These include removing malicious service links from search engines, issuing warnings through blockchain channels, and targeting individuals searching for such tools online. The continued collaboration among global agencies underscores the growing urgency to address the rising threat of easily accessible cyberattack services.