A newly identified threat group tracked as UNC6692 has been observed using a combination of email bombing and social engineering to deploy a custom malware framework known as “Snow,” according to researchers from Google Threat Intelligence Group.
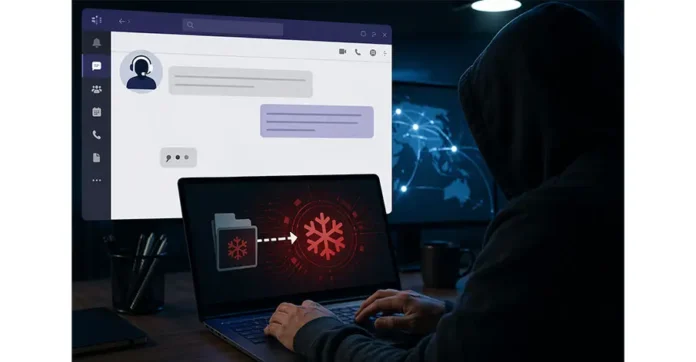
The attack begins with an email bombing campaign, where victims are flooded with a large volume of spam messages to create confusion, urgency, and distraction. Shortly after, the attacker contacts the target via platforms like Microsoft Teams, impersonating IT helpdesk personnel and offering assistance to resolve the issue.
Victims are then tricked into clicking on a malicious link disguised as a “mailbox repair” or spam-filtering tool. The phishing page mimics a legitimate utility and prompts users to perform a “health check,” during which fake authentication screens are used to capture login credentials.
In the background, the attack silently downloads and executes AutoHotKey scripts that install the first stage of malware, known as Snowbelt. This component operates as a malicious browser extension, providing attackers with initial access and persistence within the system.
Once established, Snowbelt facilitates the download of additional modules, including Snowglaze and Snowbasin. Together, these components form a modular malware ecosystem: Snowglaze enables covert communication through encrypted tunnels, while Snowbasin acts as a backdoor for executing commands and moving laterally across the network.
Researchers noted that the campaign demonstrates how attackers are evolving traditional techniques by combining psychological manipulation with trusted enterprise tools. By exploiting platforms like Microsoft Teams—often perceived as safe internal communication channels—UNC6692 is able to bypass conventional email-based security defenses and gain deeper access into corporate environments.
The attack highlights a growing trend where threat actors rely less on technical vulnerabilities and more on human behavior, using layered social engineering tactics to infiltrate organizations and deploy advanced, multi-stage malware frameworks.