
Research shows that the global digital transformation market is expected to grow to $1,009.8 billion by 2025 from $469.8 billion in 2020. At the same time, 87% of business leaders think that digital transformation will disrupt their industry. Invariably, adoption of technology levers like IoT, AR/VR, AI/ML, automation, etc. has been on the rise for organizations across the globe. This technology adoption has been accompanied by an increased interest and business need for organizations to focus and double down on their security considerations to ensure business resilience and continuity.

With new technology adoption, more sophisticated and powerful digital security threats are surfacing for organizations and CXOs must focus on strengthening their entire security ecosystem because an enterprise is as vulnerable as its weakest link. Thus, a concentrated focus on improving process, infrastructure, people, and the external ecosystem is the need of the hour to ensure enterprise threat prevention/ protection to ensure business optimization in the technology age.
Changing security risks and threats
At present time, or should I say in the 21st century, the demand and expectation from the security landscape is continuously growing, with new threats coming to the forefront every day.

| Click to enlarge |
The rise of automated phishing tools and crypto mining software present new challenges for organizations, that are changing the nature of risks and threats presented. Furthermore, concerns along the lines of governance, risk, compliance, security, privacy, cryptography and ESG measurement need to be acknowledged, rigorously reviewed (at periodic interval) and progressively update to match the threat landscape, technology changes, regulatory requirements as well as taking into consideration of our next generation’s future.
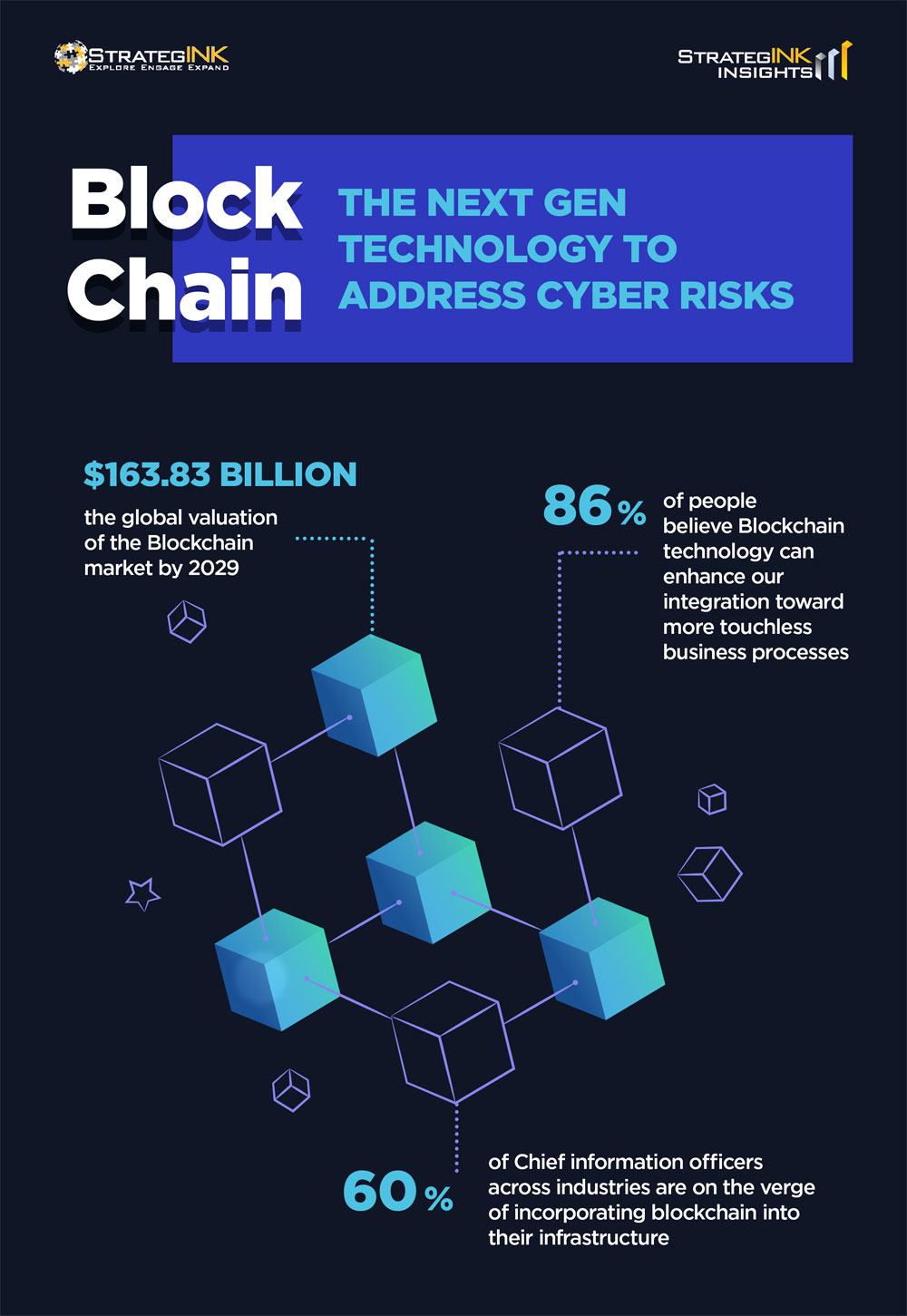
Blockchain: The next gen technology to address cyber risks
Clearly, no “one” technology and/or measurement can solve or address every single security concern out there but with exploration, research, and progressive innovation, we are working towards the goals. Invariably, the recent years have seen a rise in Blockchain technology as the next gen tech to address digital security threats and facilitate business resilience.
Blockchain is a type of distributed ledger technology that consist of growing list of records (called blocks) that are securely linked together using cryptography. It transforms how data is stored and acted upon. It can also help with reducing the carbon footprint where lesser facility and/or hardware are required to run its services.
Many would have heard of, hands-on (to a certain degree of usage), and investigated the benefits of such invention. As a matter of fact, blockchain has become popular through the promotion and investment of digital assets whereby it is used as the main backbone by cryptocurrency speculators.
| Click to enlarge |
Blockchain itself has a good potential and with right amount of usage, research, regulation, and security measurement put in place, we would be looking at the future whereby it will solve and/or address multiple concerns that humanity is currently facing.
Blockchain adoption across sectors
Here are the top use cases for Blockchain across key sectors of the economy.
- Banking: Banks are working in building central banks digital currencies (CBDC) whereby it will help to resolve cross borders payment concerns;
- Education: Tertiaries are working on a global database whereby graduates around the world can easily validate their credentials.
- Travel: Travellers relying on blockchain enabled apps on booking their next lodging and commuters using blockchain enabled apps to take ride anywhere in the world.
- Real estate: Making real estate transactions safer where smart contracts can help high value assets be tokenized and traded as cryptocurrency, followed by liquidation post sale.
- Healthcare: Faster and more accessible healthcare with secure patient/ medical data management as well as medical inventory tracking and monitoring.
All these can be track on a public ledger, which can be validated by other nodes to make sure that there is no corruption in the network.
Check out this article to learn more about Blockchain technology and its applications
Opportunities and concerns for application of Blockchain
As good as it sounds and can be practically leverage on, there are still concerns over blockchain technology. Vulnerabilities such as endpoint vulnerabilities, public and private key security, vendor risks, untested at full scale, lack of standards and regulation and untested code. The other concern to take note of is that the current blockchain technology could be crack by using quantum computing leading to massive thefts and major disruption.
Endpoint should have layers of security measurement to prevent and protect it, cryptographic keys should be kept in a secured vault, vendor should also put in place stringent GRC, bug bounty program, insurance and constantly testing their security measurement, full scale testing requires the collaboration of govern body and commercial providers, standards and regulation should be draft and gazetted at both regulators and judicial level, and code should be thoroughly tested.
Lastly, blockchain technology should be built on top of quantum computing to leverage on its power and also its resiliency and cryptography capabilities.
Thus, as the nature and magnitude of cyber risks are constantly changing with the deployment of different technological advances, there is a need to have an equivalent focus on deciphering new ways of security our systems, businesses and countries and redefine future of security at every step.
Essential guidance for CXOs to facilitate digital security
From a CXO standpoint, there are four levers that need to be focused on to enhance security in this digital age:
- Invest in secure infrastructure, devices and hardware and software to tackle instances of end-point security
- Facilitate employee training and upskilling to effectively utilize the secure infrastructure as well as ensure high levels of awareness about potential threats and mitigation strategies
- Create robust processes and disaster recovery strategies to ensure business continuity
- Ensure external stakeholder threat prevention, especially across different vendors and partners, who may have access to sensitive information for your enterprise





